Part 1 of 3: Access is just where the crisis starts.
A Fortune 500 CISO asked me last month: “How do we give our AI agents the right access?”
It’s the wrong question. Yet it’s the most common question I’ve heard in the last year. Because that one question is actually three questions collapsed into one. Each one harder than the last.
I build identity security products for the world’s largest enterprises. Over the last year, every conversation has shifted from “how do we manage employee access?” to “how do we manage agent access?” The frameworks we’ve built over two decades of IAM don’t survive contact with agents. Here’s why.
When you try to solve identity for AI agents, you are answering three distinct questions:
1. Access – What can an agent do?
2. Auth – Who authorized the agent and how?
3. Intent – Why did the agent act?
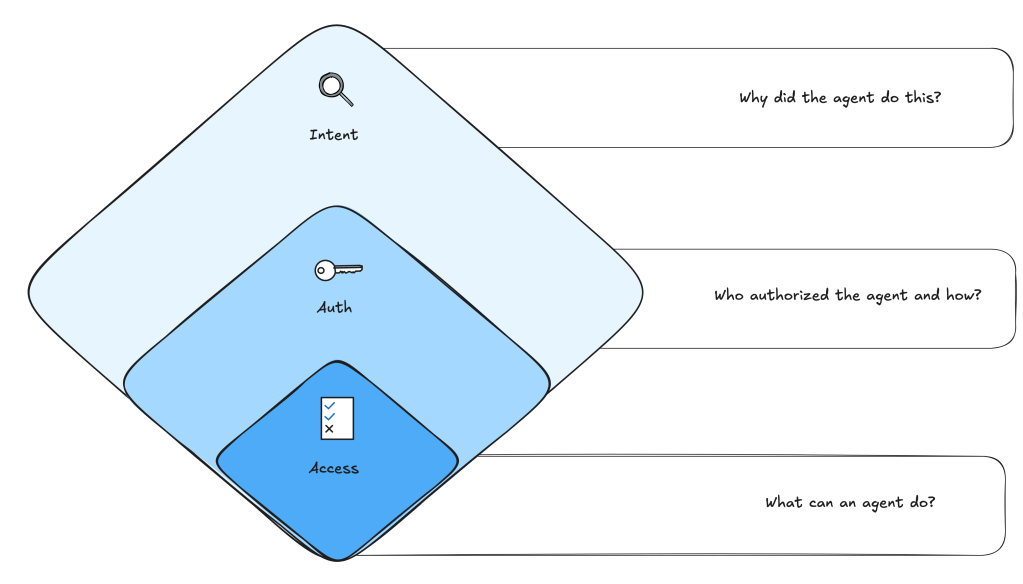
These aren’t just questions. It is a maturity model. Organizations that haven’t answered Question 1 cannot meaningfully answer Questions 2 or 3. I’m writing a series highlighting the crises at each stage. This piece covers Access.
Question 1: Access – What Can An Agent Do?
The access problem feels familiar: scope the permissions, define the boundaries. We’ve been doing this for humans for twenty years. Easy.
Ha! But agents break the model immediately. When humans access 1500 apps/actions in an hour, it’s flagged as a risk (data exfiltration, compromised creds, insider threat). When an agent calls 1500 tools, it’s just doing its job (pulling contacts, cross-referencing records, generating/updating reports). The exact behavior that triggers an alert for humans is just another Tuesday for an agent.
Our risk-scoring and behavioral models aren’t slightly wrong for agents, but architecturally wrong. The signal and the noise have swapped.
Even Fortune 500 companies with strong human-focused controls are perplexed. They are retrofitting their Service Account IAM policies onto AI Agents. This doesn’t work. Agents aren’t service accounts. A service account does the same thing every day, an agent’s behavior is emergent. It varies by task and by context.
Before agents, the non-human identity problem was already overwhelming. Agents made it absurd.
The direction is clear: Zero Standing Privileges.
I know, I know, it feels like it’s 2017. Agents only get the exact permissions needed for the exact task they’re performing, then permissions are auto-revoked when the task is done. Not scoped broadly like adm- or a* accounts. Not long-lived like service accounts. Exact and ephemeral access.
This is where we need to be. Almost nobody is there.
Access is just where the crisis starts. Next in the series: Agent Auth
